Documentation Index
Fetch the complete documentation index at: https://developer.prove.com/llms.txt
Use this file to discover all available pages before exploring further.
Prove Pre-Fill for Consumers solution
The Prove Pre-Fill for Consumers solution streamlines online account creation by automatically filling forms with bank-grade verified consumer data via phone number. Architecturally, possession of the number comes first: Prove only releases verified attributes once the session has established enough assurance that the consumer controls that line—so pre-fill is tied to network- and policy-backed identity, not self-typed form data alone.Concepts and definitions
To better understand the core components of the Prove Pre-Fill® solution, here are the key concepts and terms used on this page:- Mobile Auth℠: A technology that discovers and verifies a consumer’s phone number silently behind mobile network firewalls, providing protection against device-based fraud like cloning or emulation.
- KYC (Know Your Customer) Add-On: A compliance layer that screens data against anti-money laundering (AML) lists and validates consumer information against more than 1 data source to support Customer Identification Programs (CIP).
- Possession Check: The process of verifying that a user is in physical control of the given phone number, conducted via Mobile Auth, SMS OTP, or Instant Link.
- Instant Link: A fortified link sent via SMS to desktop users to complete a possession check by leveraging the mobile network’s authentication.
Global availability
Prove Pre-Fill is available in the following regions:- The United States with its territories
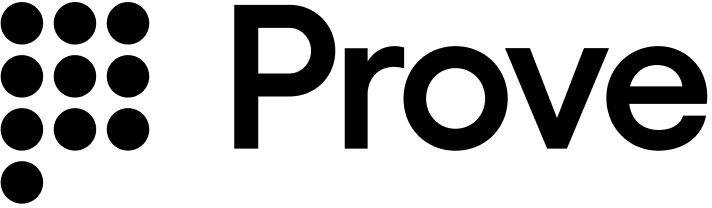
Prove Pre-Fill flow
Prove Pre-Fill® with Mobile Auth flow
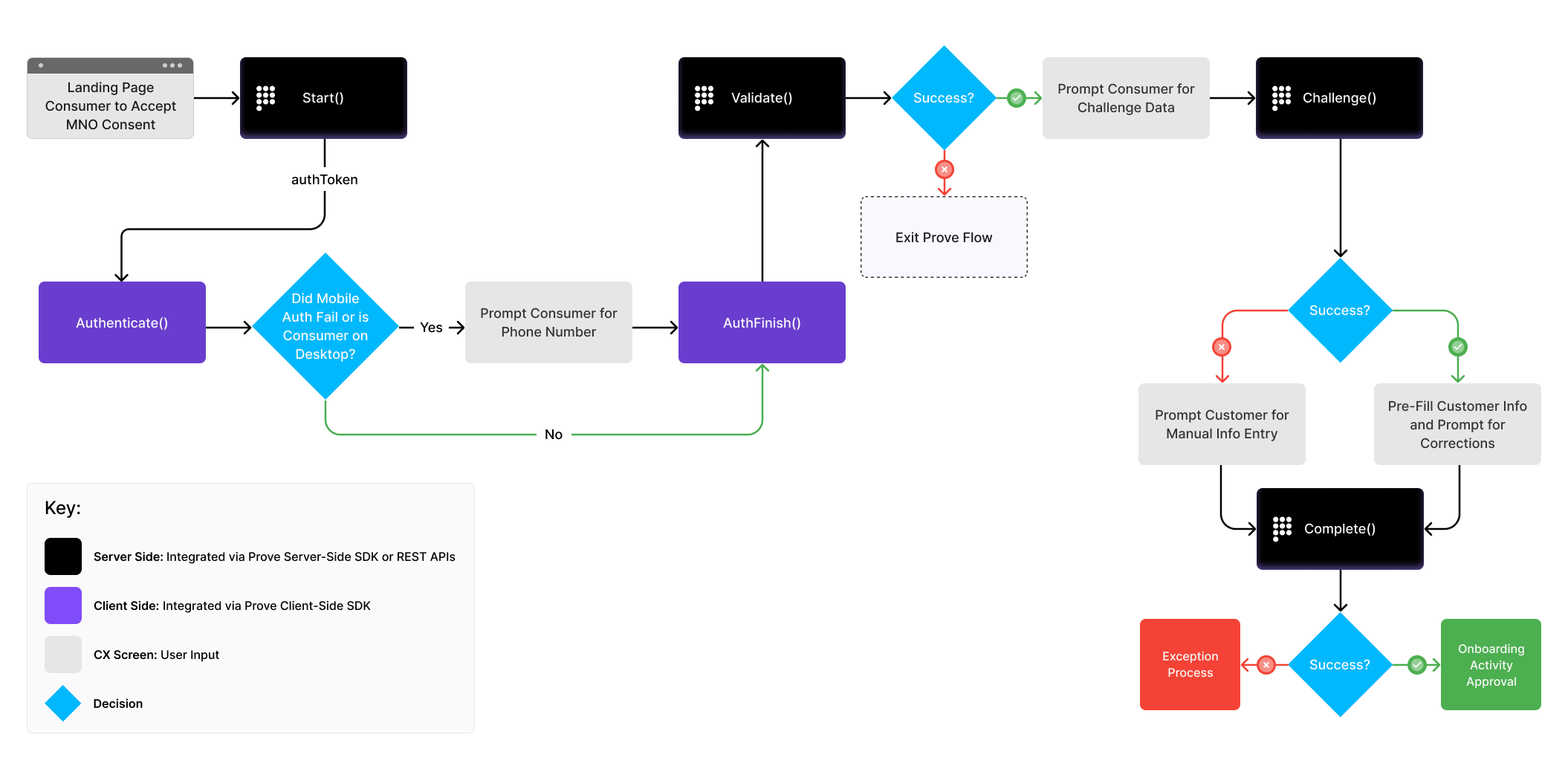
- Session start — Opens a guarded session and records whether the consumer is on mobile or desktop, because the viable possession paths (silent network authentication, SMS one-time passcode, Instant Link) depend on that context.
- Possession — The consumer demonstrates control of the number. On mobile, that often means SMS OTP by default, with optional silent Mobile Auth and fallback to OTP when needed. On desktop, possession typically uses Instant Link: an SMS that moves the user into the mobile environment where the number can be asserted.
- Validate — Confirms that the phone number can be authenticated in light of the possession proof before Prove deepens into identity assertions.
- Challenge — Checks whether the identity attributes for the session meet the trust bar to proceed—that the data hangs together with sufficient assurance.
- Complete — Confirms in real time that the identity information matches the mobile number so your application can treat the result as suitable for bank-grade pre-fill.
Later stages surface policy and fraud outcomes via the Global Fraud Policy (GFP) evaluation so you can interpret not only pass or fail, but why.